bhtooefr
TDIClub Enthusiast, ToofTek Inventor
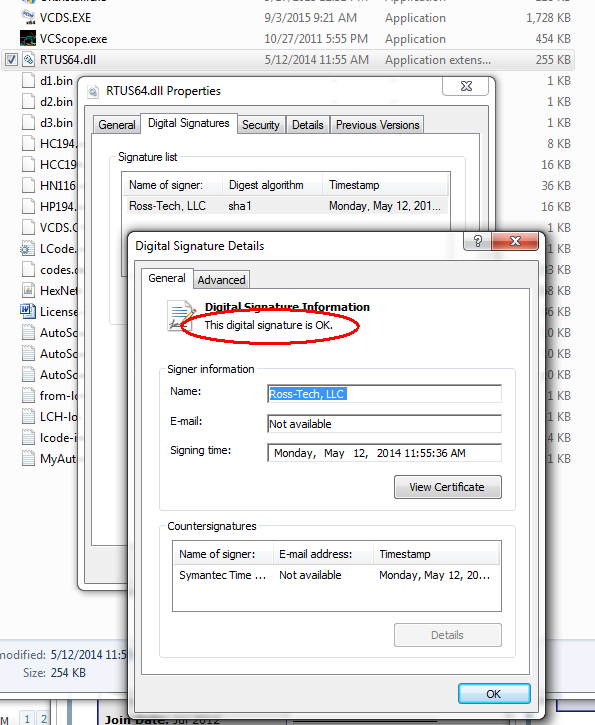
Earlier this month, three Hungarian researchers did a talk at Hacktivity 2015 on potential attacks against cars by installing malware on PCs used to do OBD diagnostics. They used an Audi TT in the proof of concept, running VCDS (although they didn't name it - probably because, for "a few tens of dollars", they were likely running a pirated version) on the PC in question, and demonstrated that they could silently do things like disable airbags. They did not directly attack VCDS, but rather performed replay attacks based the communications that VCDS would make, sitting in between VCDS and the FTDI driver with their malware.
This is not something to panic about, but there are some things that would be wise to consider in light of this.
This is not something to panic about, but there are some things that would be wise to consider in light of this.
- Ensure that any computer that touches a car's data link connector is receiving regular security updates. (Read: stop running XP, it's time to upgrade!) This includes phones and tablets, too, if you're using VCDS Mobile, Torque, or any other diagnostic product. (Read: keep that old tablet that's stuck on Android 4.0 far away from your car's data link connector, and I'd honestly be leery of any iOS devices that can't run iOS 9, based on Apple's current security policies of only reliably supporting the current version of an OS.)
- Ensure that you have antimalware software installed on any computer that touches a car's DLC. Microsoft offers Security Essentials for Windows Vista and 7, and Windows Defender is included with Windows 8 and 10.
- If you absolutely must use a machine that no longer has security updates available (for instance, a machine running Windows XP) for car diagnostics, make sure that the machine is never connected to any networks, and do not connect untrusted media (thumb drives and the like) to it.